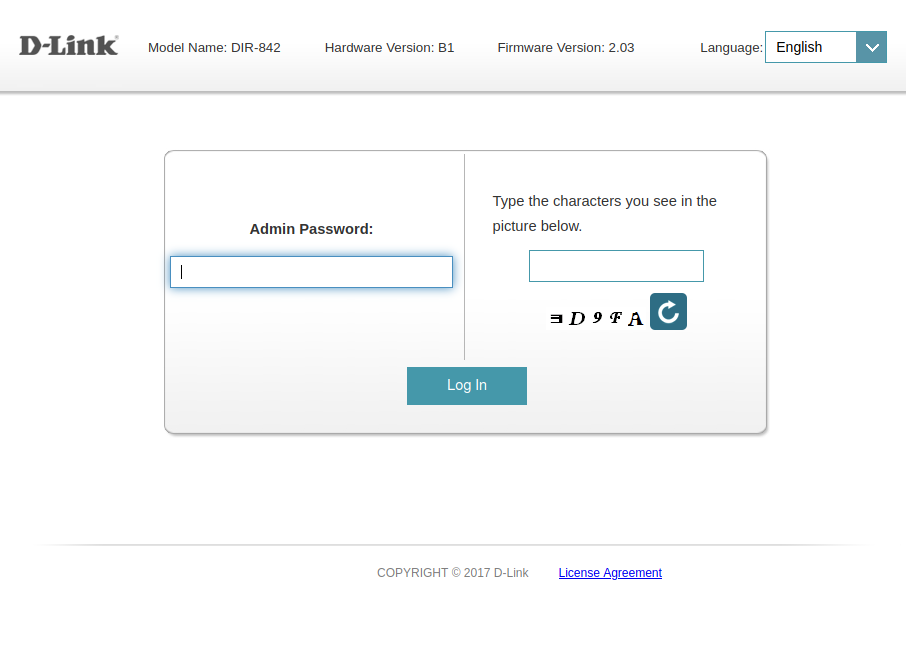
D-LINK DIR-842 Rev-B privilege escalation
In this quick blog post we’ll see how to enable Telnet on your DIR-842 rev-b
Read More
4 min read
In this quick blog post we’ll see how to enable Telnet on your DIR-842 rev-b
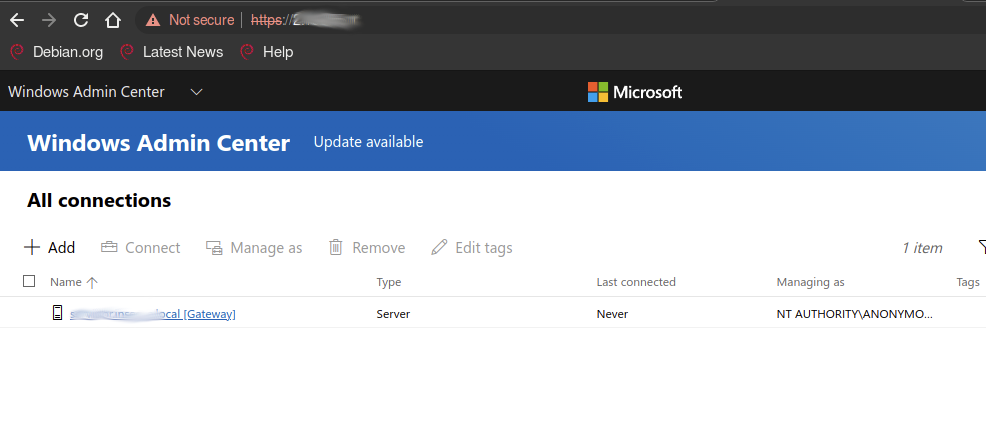
Exploring the so-called NTLM ANONYMOUS_LOGON user through HTTP endpoints.
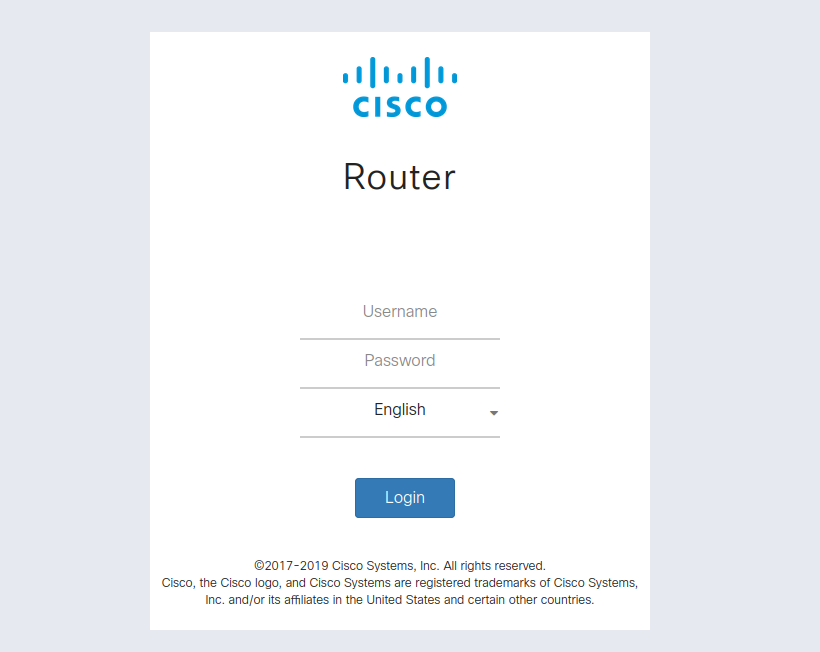
A quick research into remotely identifying Cisco’s RV43Xs
Take a look at our new mapping feature, visualize and make sense of Internet resources in a blink !

Cristi made us a tutorial video!
Go check it out and learn about filters and reports !